This piece might ruffle a few feathers. That’s because there’s a lot of people out there that think having an Airgap Wallet makes their setup super secure and basically hacker proof, but they’re wrong.
One of the most common ways people fail at security is by thinking that something is secure… when in fact it’s not. So today we’re going to explain what Air Gapped Hardware Wallets are and cut through the often incorrect or just misleading marketing that many Hardware Wallet vendors push to make sure you’re protected.
Contents
What Does Airgap Mean?
An air gapped device is one which has no network interfaces, either wired or wireless, connected to outside networks.
Many computers, even when they are not plugged into a wired network, have a wireless network interface controller (WiFi) and are connected to nearby wireless networks to access the Internet and update software. This represents a security vulnerability, so air-gapped computers either have their wireless interface controller permanently disabled or physically removed.
Wikipedia
Rather than transferring data using a USB cable or Wi-Fi, you have to physically write the data to a drive of some sort (microSD card, USB flash drive, HDD etc) and physically walk it to the air gapped device.
The point of this is to create a literal air gap between the device and fully control all data flowing in and out. Data is only transferred if the person physically moving the data is authorized to do so, and that data has been properly vetted.
In traditional IT environments like an office with employee computers and more securely protected servers, this is one of the top security measures that protects outside hackers from stealing sensitive data.
It’s also common for these air gapped computers to be in much more physically secure locations with more locks, more guards, less access to non-authorized people and so on. This cuts off the low secure area (general plebs in an office) from the high secure area (highly locked down server rooms).
What Is An Airgap Wallet?
Now that we understand what air gap means, let’s have a look at how this is treated in the world of hardware wallets.
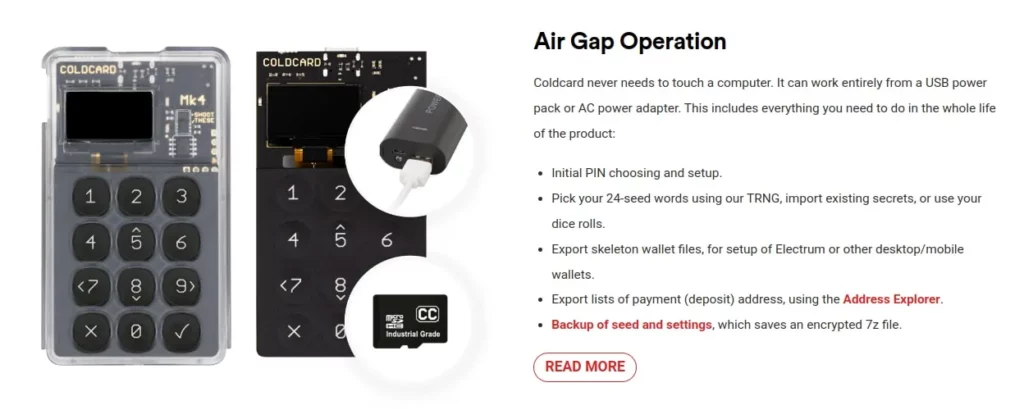
In the world of crypto wallets, an Air Gapped Wallet is one that’s (usually) completely disconnected from any computer or network such as the Internet. They are generally never plugged into the computer and instead communicate by passing microSD cards back and forth or by scanning QR codes.
One of the most popular examples of a Hardware Wallet that supports air gapped transaction signing is the COLDCARD Mk4. Importantly there are many hardware wallets out there that claim to be air gapped, but still need to be plugged into an internet connected computer from time to time.
As we noted in our Bitcoin Security guides, the best way to protect against a security risk is to completely remove it. But. While you might think having your wallet air gapped completely removes the risk of hacking, it doesn’t. In fact, sometimes it can make security worse if it’s not implemented properly..
How Do You Use An Air Gapped Wallet To Send Bitcoin?
Although the Hardware Wallet is completely disconnected from the Internet or any other computer, data still needs to flow back and forth between the Hardware Wallet and the Computer if you ever want to spend your bitcoins. This is because the Hardware Wallet is what’s used to sign the transaction and prove that you own the bitcoins you’re spending.
So let’s look at how most air gapped crypto wallets operate today when you want to create and broadcast a Bitcoin Transaction:
- Create Transaction: The computer creates an unsigned transaction which is called a Partially Signed Bitcoin Transaction (PSBT) as defined by BIP174
- Save PSBT: This PSBT transaction data is saved to a microSD card
- Transfer PSBT: You move the microSD card from the computer to the Hardware Wallet
- Sign PSBT: The Hardware Wallet uses your Private Key to sign the PSBT
- Transfer Signed Transaction: You again move the microSD card back to the computer
- Broadcast Signed Transaction: Now that it’s a fully signed transaction, the computer broadcasts it to the Bitcoin network
Why Air Gapped Hardware Wallets Don’t Increase Security The Way You Think
While “not being connected” sounds pretty logical and bullet proof at face value, data is still being transferred back and forth between this “untrusted computer” and the air gapped Hardware Wallet.
It’s just using a microSD card and you as the transfer medium rather than a USB cable. The key thing to point out here, the reason why having an air gap doesn’t increase security in the way most people think it does, is this:
The security of the Hardware Wallet depends on how it sanitizes and checks the integrity of the data being transferred. Not how that data is transferred.
The untrusted computer can put a giant ass virus on that microSD card and when you plug it into your “totally hacker proof air gapped crypto Hardware Wallet” it’ll still infect it. This isn’t a perfect analogy obviously, but it helps to make the point clear. It doesn’t matter how the data gets there… it’s what the data is and how it’s vetted that’s important.
There’s multiple different ways to transmit the data to/from a Hardware Wallets such as:
- USB Cable: The traditional data transfer method
- USB Drive / microSD Card: Use microSD cards to transfer the data
- NFC: Uses the Near Field Communications standard to transfer the data
- QR Code: Uses a QR code to encode the data, the Hardware Wallet then takes a photo of it
- Bluetooth: Uses Bluetooth standards to transfer the data, popular with mobile wallets
Whether you’re transmitting data to the Hardware Wallet via QR Code, microSD card or a more normal (non air gapped) USB connection there is still data going back and forth. If someone infects your computer and takes control of your software wallet, it won’t matter how the maliciously created transaction data is transferred to the Hardware Wallet.
What matters is how that Hardware Wallet receives, inspects and sanitizes the data. If it’s not doing this, an air gapped Hardware Wallet can 100% still get hacked, so be sure to understand that something being “air gapped” doesn’t make it bullet proof.
Just with any other type of security, having an air gap wallet is not a panacea and doesn’t just magically make your crypto “hacker proof”. An internationally famous example of air-gaped computers getting hacked was the Stuxnet malware that took down a uranium enrichment facility in Iran in 2010.
New to Athena Alpha? Start today!
How Air Gapped Wallets Actually Increase Security
In order for a Hardware Wallet to be classified by us as being air gapped, it must be usable from start to finish in a totally separate location to the software wallet and computer it resides on.
For example imagine a Hardware Wallet that’s kept in a Faraday bag, that’s then locked in a safe which itself is hidden in an area of the house with a much more sturdy, locked door. The room has no windows, no cameras and no other computers. The hardware wallet always stays in this higher security area and never leaves.
You should be able to perform its initial setup, create/import/restore a wallet, display receive addresses, sign transactions and upgrade its firmware all without it ever having to leave this higher secure area.
Now, to better understand how air gapped wallets compare to ones that aren’t, let’s go through some key points.
No USB
USB is a huge, old standard. As such it takes a lot of time, skill and money to properly test and secure it due to all the complexities and the fact that it just wasn’t ever designed as a secure transfer protocol. This results in many manufacturers releasing hardware wallets that don’t use it securely.
Chief among this is using End-To-End Encryption (E2EE) when transferring data to and from the hardware wallet. If a vendor doesn’t use E2EE, then any programs or even browser websites can see this data and even change it in real time as it’s sent via USB.
While some use full E2EE for data transfer, many don’t or do not provide their code to verify they do so in a safe manor. This can result in transaction details, wallet information and more being exposed to the computer or worse, being altered in real time by malicious applications.
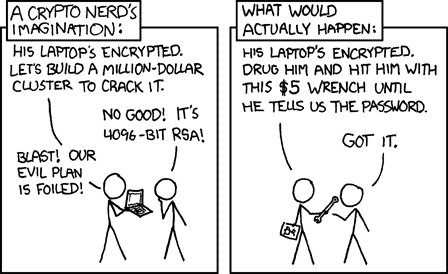
USB can also leak information about your hardware wallet via the ID’s that manufacturers use. If your computer is compromised and knows that you’ve connected a Ledger 1234, then so does the attacker who might now come knocking on your door with a $5 wrench.
As air gapped wallets don’t use USB, they help mitigate these security issues. While it’s true that microSD cards do still require software library dependencies and also have a micro-controller inside them that can be hacked, it’s a smaller attack surface in general and more importantly, you can just buy 20 microSD cards from 20 random shops to ensure you’re not using a compromised one.
You can also use two different microSD cards, one for the unsigned transaction and the other for the signed transaction. This way both cards have to be compromised in order for the attack to succeed.
No QR Codes, No NFC, No Bluetooth
QR codes require camera hardware (again with micro-controllers in them) as well as external software library dependencies to read in the picture, analyze the QR code etc.
This is the same with NFC and Bluetooth is even worse as you not only have library dependencies and all the security risks that come with Bluetooth in general, now your device is broadcasting itself to the world over tens of meters.
NFC has also been shown by security researchers to be able to transmit data at a much longer range than expected, up to 100 meters, using an exploit called NFCdrip.
More to the point, these all require you to bring a non-secure device (mobile or laptop) into the high secure area to scan back in the signed QR code or communicate via NFC/Bluetooth. In general it’s not wise to bring insecure devices into special, high security areas as there’s just endless ways things can go wrong.
On top of all this, updating firmware over QR code, NFC or Bluetooth is either impossible or again requires a non-secure device to be in the high secure area. A proper air gapped wallet that stays in its secure location and only has data transferred to/from it via microSD card minimizes a huge amount of potential risks.
Physical Security
But by far one of the biggest benefits of an air gapped hardware wallet is the additional physical security it allows for.
Hardware wallets that are constantly moved around insecure areas are more exposed and leak more information than ones that are permanently stored in a secure area. Maybe you leave it on your desk. Maybe someone sees you using it through a window. Maybe a webcam on a compromised device captures you using it. Maybe you lose it while transporting it.
There’s a million bad possibilities.
Being fully air gapped enables you to never have to move the hardware wallet outside its high security area. This can scale up to full on businesses or individuals that custody millions or billions with the hardware wallet never leaving bank grade facilities with armed guards, sealed vaults and more.
How Air Gapped Wallets Decrease Security
Security is rarely, if ever, perfect though and as such, air gapped wallets do introduce a few things that actually decrease security.
False Sense Of Security
For hardware wallets that don’t implement full air gapped capabilities like what we’ve described above, which is many, it can trick the user into a false sense of security by making them think their device is 100% protected when it’s not.
We mostly blame companies that market their products improperly and butcher what “air gapped” actually is for this. Having to constantly plug your hardware wallet into a internet connected computer to update its firmware and only being able to sign transactions via Bluetooth isn’t what we’d consider a safe, air gapped hardware wallet! But that doesn’t stop them from advertising it as so.
People that aren’t technically savvy can see this slick marketing and think that they’re invincible… until all their funds disappear because their phone was compromised and the hardware wallet didn’t properly validate that the change address belonged to the user.
No Anti-Klepto Protection
Anti-Klepto is a protocol that stops hardware wallets from secretly leaking you private keys via the transactions you sign and broadcast. In order to protect against it, an air gapped wallet would have to perform two full rounds of transferring the transaction data back and forth between the computer and hardware wallet.
As this further complicates the already slow workflow, it isn’t implemented in any air gapped hardware wallet as far as we’re aware. If you’re connected via USB, the hardware wallet and software wallet can seamlessly communicate back and forth, following this protocol.
The BitBox02 has this protection in place already where as many others do not.
Decreased Usability
Finally most air gapped wallets by their very nature add multiple additional steps into the operation of the device that can introduce user error. Try as we might, we’re all only human and whether it’s due to not paying attention, laziness or just not being bothered steps can be missed or performed incorrectly.
Complexity is the enemy of security and adding more steps and more microSD cards, especially for less technical users, can result in potential mistakes and lost funds.
For example, you might use one microSD card to transfer data back and forth to your air gapped hardware wallet constantly as well as keep other personal documents with your name and address on it. At some point, you accidentally lose the microSD card while out and now potential attackers know your wallet info and address.
While this scenario might sound silly to some, keep in mind millions still use post it notes to store their passwords on their monitors. People are not perfect. While a USB connection might be less secure in some ways, it can also be more secure in that with a simple click, a number of steps are removed from the work flow.
The Athena Assessment
To be clear, for the vast majority of users it likely isn’t going to make a significant difference whether their wallet supports air gap operations or not. There are just so many other factors that are more important such as being able to see the source code as well as proper seed generation and storage. Any of our top wallets will be fantastic for 99.99% of users as they ensure these key features and more are present.
Overall we judge a hardware wallet that can perform all main functions while being locked in a bank vault for its entire life as more secure than one that requires a USB connection. But that doesn’t mean something like the BitBox02 that is USB only is a bad Hardware Wallet.
Also a hardware wallet manufacturer claiming that their wallet is “air gapped” doesn’t make it hacker proof and it might not even be a fully air gapped device. If you are one of the few that really wants to take advantage of a properly air gapped wallet we’d recommend you ensure it:
- Lives its entire life in a higher security area, such as inside a Faraday bag that’s kept inside a safe that’s hidden somewhere in a locked area of the house. The more cameras, guards, locks and steel the better
- Can live and fully operate, permanently, in its high secure area and is never removed
- Can perform all functions using a microSD card without being connected to another device
- Can properly verify and sanitize any information that’s given to it over the microSD card such as change addresses, firmware keys, receive addresses etc
- Is used with known brand, randomly store bought microSD cards that are only used for it and nothing else
- Meets as many of our other Security & Privacy tests listed under our Rating Methodology
As you can see, proper air gapped operation is quite a lot more involved than what the marketing might claim. This increased inconvenience does add security, but if you’re not planning on doing something similar to the above, then perhaps air gapped is not for you. Which is fine.
We’re of the belief that good hardware wallets should support these types of operational modes so that the user can grow into them as their needs evolve. But not being air gapped doesn’t make for a bad device either, just slightly less secure.
Security is about creating multiple layers of protection around your private keys. If one line falls, there should be 10 others ready and waiting. Operating in air gapped mode can absolutely be one of these layers of defense, just make sure the other 9 are there too or else you’re going to get rekt air gapped or not!
More Security Info
- A Beginners Guide To Bitcoin Security
- A Guide To Advanced Bitcoin Security
- A Guide To Expert Bitcoin Security
- Hardware Wallet Risks
- How To Protect Your Crypto
- How To Protect Your Bitcoin Private Key
- Bitcoin Scams: How To Spot And Avoid Them
FAQ
Is Ledger Air-Gapped?
No. Ledger doesn’t support air-gapped operation and requires a USB connection to operate. We also do not recommend readers buy or use a Ledger as it doesn’t meet our security and privacy standards.
What Is An Air-Gapped Key?
An Air-Gapped Key refers to a Private Key that is stored on a air gapped Hardware Wallet. This usually means it is never physically plugged into a computer via a USB cable.