Welcome fren! Last week we released our free Beginners Guide To Bitcoin Privacy. Now everyone has $0 access to simple and straightforward expert advice when it comes to Bitcoin privacy. For a lot of you though, these basic steps aren’t really enough. You want the absolute best privacy that Bitcoin has to offer which is what we’ll be covering today in our advanced bitcoin privacy guide.
If you think mainstream medias coverage of beginner Bitcoin privacy is bad, don’t even get us started on their advanced levels! For the most part, it just doesn’t exist. At best they’ll tell you to “get a Ledger crypto wallet” which has terribly poor privacy and security and call it a day.
Many of these mainstream media sources are also centralized, KYC Crypto exchanges that don’t want you to have privacy (as then they can’t sell your data) and also regularly try and convince you to go gamble on their shitcoin casinos.
So let’s learn how to do it right.
Note: This Privacy guide is for “Advanced Levels” which are people with “Savings Account” level funds. If you’re securing larger amounts, please see our Expert Bitcoin Privacy level guides
Contents
Key Advanced Bitcoin Privacy Points
- Beginner Privacy: Ensure you do everything in our Beginners Guide To Bitcoin Privacy
- Use A Hardware Crypto Wallet: Don’t buy it with your real world identity
- Use Your Own Full Bitcoin Node: Build or buy your own node and connect all wallets to it
- Use Tor: Ensure your node and all wallets only connect over Tor or a private VPN
- Use The Lightning Network: Use a separate wallet over Lightning to purchase daily goods
- Use Coin Control & Labeling: Label and be selective about which sats you spend
Advanced Bitcoin Privacy
Firstly, you can get a full run down on what each of our levels entail and where you might fit into them by looking at our Understanding Bitcoin piece or this overview table below. For this advanced Bitcoin privacy guide we are only targeting people in the Advanced and Expert levels.
| Level | Beginner | Advanced | Expert |
|---|---|---|---|
| Funds Amount | Pocket Money | Savings Account | Serious Investments |
| Exchange Type | Non-KYC | Non-KYC | Non-KYC |
| Wallet Type | Software (Hot) / Hardware (Cold) | Hardware (Cold) | Hardware (Cold) |
| Signature Type | Single Signature | Single Signature | Multisig |
| Key Custody | Self Custody | Self Custody | Self Custody |
| Key Backup | Laminated Paper | Laminated Paper | Metal Seed Plate |
| Key Locations | 1+ | 2+ | 2+ |
| Key Security | None | Fire Proof Safe | Multiple Methods |
| Own Full Node | No | Yes | Yes |
| Electrum Server | Public Electrum toggle_on | Private Electrum toggle_on | Private Electrum toggle_on |
| Tor | No | Yes | Yes |
Our top priorities for this site is to help everyone learn how to safely and privately buy, use, invest and grow wealthy with Bitcoin, so also know that this piece is just the start of our privacy information. We’ll be adding and expanding on each of the below points in much more detail as time goes on.
From in depth investigations into the pros and cons of various hardware crypto wallets to step by step setup guides for wallets and node builds, we want to ensure everyone gets the best information out there.
Use A Hardware Wallet

Whether you’re in the Advanced or Expert stages of your Bitcoin journey it’s highly likely that your bitcoins are worth a reasonable amount. If you don’t want to lose them, you should absolutely be buying a dedicated hardware wallet. These are physical devices in meatspace that do one thing, generate and secure your private keys.
You never want your private keys touching that revolting, malware infested computer/phone of yours trust us. Hardware wallets are cheap ($50+ USD) and easy to setup and use. Our top recommendations include:
These are the highest rated hardware Crypto Wallets that we recommend, but there are many more. While you’re welcome to buy any hardware wallet you think is appropriate, we’d only advise it after considerable scrutiny. Here are a few major considerations you should weigh up before just purchasing any random device you find on the internet:
- True Randomness Generation: It should uses two independent sources of randomness (or more) for your private key generation. One of the main purposes of hardware crypto wallets is to generate your private keys, this needs to be next level grade bullet proof! A poorly generated private key is a huge security hole
- Open Source: Its code should be 100% viewable for you or any other security researcher to review and interrogate. Open source code, vetted over many years is one of the top ways to ensure a secure environment. Source available is the bare minimum
- Verifiable Software Binaries: It should have verifiable software binaries and PGP key signature checking with easy to follow instructions on their website. This allows you to verify that the software you’re downloading from their website hasn’t been maliciously altered or tampered with
- Uses Interoperable Standards: It should use common, industry standards such as BIP-0039 for its seed phrase words to allow for interoperable use in case there’s any reason to migrate away from that hardware vendor (eg they go bankrupt / get taken over / start acting stupid). To help with this, check out the major software wallets out there and see which devices they integrate with
- Reasonable Company History: The company itself should have been around for at least 5 years or more and the more revisions of the hardware they have, the better (eg. COLDCARD is up to “Mk4” while BitBox is up to “02” now). This hopefully ensures (but doesn’t guarantee) that hardware level issues have been resolved at the source and that the hardware and software have had most of their main kinks sorted out. You should also review their general practices like storage of customer data, history of how they handle security breaches and how they work with the security community in general
- Works With Standard Wallets: It should work with any industry standard third party Bitcoin wallet such as Sparrow Wallet or Bitcoin Core. You should not be locked into using only their bundled software wallet program as this can be both a privacy risk and a problem if the company ever runs into troubles
- Full Bitcoin Node via Tor Support: It should fully support you connecting it to your own Full Bitcoin Node via Tor. This is vital for Advanced and Expert levels both for privacy and security
- Easy Import / Export: It should fully support importing and exporting of all required info (Including Coin / UTXO Labels) for easy backup and restore, especially across various third party wallets (eg exporting from their wallet app and importing into a third party wallet) and for Multisig wallets that require more detailed backup information than single signature ones
- Multisig Support: It should fully support Multisig Wallets as well as xPub / Watch Only wallets and this support should extend to the standardized third party wallets as well
- Labeling And Control Of Coins: It should fully support labeling of coins (UTXOs) and being able to control which coins you spend either through their own app or through a standardized third party wallet
- Purchase Only From The Supplier: It should come in a tamper evident bag directly from the supplier and no one else. Do NOT buy from other random online sellers, eBay, forums or any other source
- Consider Physical Size: When choosing a device many people prefer large screens to enable easier reading / interaction, but be aware that the larger the device is, the harder it is to store / hide. It will also likely be more expensive too
Pro Tip: Don’t buy a hardware crypto wallet with your real world identity
If the hardware wallet company gets hacked, your identity is forever linked to “this customer has so much crypto they needed to buy a hardware wallet” = huge target. A recent example of this is how Ledger had all their customer data stolen or how Trezor had a huge data leak too. Now all those people are forever at physical risk with criminals knowing the names, addresses, emails and more. Not cool!
That company may also link your identity and funds to that hardware wallet and monitor your device / addresses / balance / transactions via their software (eg. Ledger Live)… which they then pass on to governments, third parties etc.
Buying the device without revealing your own real world identity is a one time, highly beneficial security enhancement that ensures knowledge of your stash is never revealed no matter how many times they get rekt. For more security focused information you can also check out our Advanced Bitcoin Security guide.
Most hardware Crypto Wallet manufacturers will accept Bitcoin too making this a relatively easy way to protect yourself. Make up a name, create a one time Proton.me email account via Tor Browser, pay via Bitcoin you obtained via a non-KYC source and you’re set!
Use Your Own Full Bitcoin Node
Everything in Bitcoin is done through Bitcoin Nodes. If it’s not your node, then someone else knows your balance and spending info and can also feed you false information. For example they could allow a transaction that isn’t following the rules of the Bitcoin network. If you then try to spend those bitcoins somewhere else they’ll be rejected by the rest of the network.
While this is a serious security and privacy risk, the natural way that people learn about Bitcoin means that it’s not until later that they understand enough about What A Bitcoin Wallet Is, how it works and why it’s so critical to run your own node. Fear not though!
Running a node is easy, has a moderate one time hardware purchase fee ($400+ USD) and helps strengthen the Bitcoin network. They can also be used for many other purposes too such as chat and podcast servers, payment processors for business and more. If you are at an Advanced or Expert level in Understanding Bitcoin and have decent funds invested we strongly recommend building or buying your own Full Bitcoin Node.

Once your node is online it’ll take a few days to download the entire Bitcoin Blockchain (or “sync”) and then all you have to do is setup your new Bitcoin Wallet and point it at it. If you have funds in other wallets then send them across to this new one and you’re all set! Examples of fantastic nodes include:
Owning your own Full Bitcoin Node also now allows you to run your own Lightning Node. You can then connect your mobile Lightning Wallets back to it and again drastically improve your privacy and security even further. Becoming a node runner is another entire rabbit hole to go down, but a vital one.
>> Learn More: Bitcoin Lightning Node Profitability: ROI & What To Know Before Investing
Use Tor
ISPs track and log every website URL you go to for multiple years in many countries, Bitcoin transactions get broadcast out over the internet and are no different. As such, to avoid associating your IP Address and thus, your real world identity, whenever you broadcast a new Bitcoin transaction you should be setting everything up to work by default over Tor.
This is actually quite a painless part of Bitcoin privacy as all of the above wallet and node suggestions have Tor either built right into them or have simple ways of enabling it in their settings. You can also setup a VPN to shield your IP Address, but many VPN providers still log and sell your data, especially free ones so we recommend the simpler and more private Tor option.
Pro Tip: Don’t connect your wallet software to your node unencrypted, even if you’re doing this over your own private Local Area Network (LAN) / WiFi. This is because you may have other third party things secretly listening in like smart home devices or other compromised computers. Make sure your wallet software and node are connected either via RPC over HTTPS or Tor. This will ensure that your own transaction (and wallet) data is only ever sent with encryption.
Purchase Via The Lightning Network
One of the biggest risks to your privacy with Bitcoin is when you make a purchase. This is because you’ll usually be interacting with a business and businesses like to scoop up as much data on their customers as they can (not us though).
They also prefer to partner with other businesses to help do various things, like accepting Bitcoin payments, rather than implement it themselves. This all leads to the tracking and selling of your personal and financial data which is no está bien.
Beyond this privacy reason, purchasing goods and services with Lightning is faster and will save you a bunch in on chain Transaction Fees. While this wasn’t really possible just a few short years ago, the Lightning Network now has hugely increased its liquidity meaning it can handle most small and even medium sized transactions
Pro Tip: Be sure to open your Lightning channels during low fee times. This helps reduce costs and as opening new channels isn’t usually a time sensitive thing, there’s no reason to do it at peak times. Once open, you can then use that channel for years!
Use Coin Control & Labeling
Coin Control (also called segregation sometimes) is the ability to specifically select which coins or Unspent Transaction Outputs (UTXO’s) that you want to spend. In order for this to be properly useful you usually want to also label your coins as well. This then allows you to keep track of where those coins came from (for example from a KYC or frowned upon source) and thus only spend them when it’s appropriate.
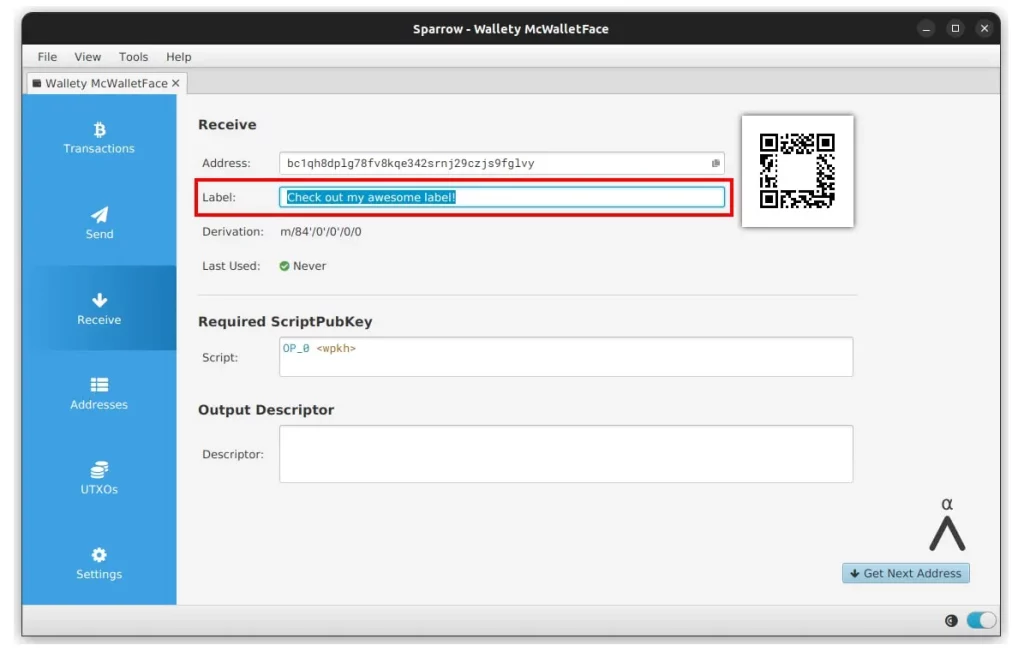
This labeling and control becomes important if you have a mixed stack of non-KYC and KYC sources or if you’ve completed any CoinJoin type transactions which we’ll cover below. As every UTXO is easily traced via the blockchain to its historic transactions, Coin Control is an important part of your privacy. Why?
Imagine if you started out your Bitcoin journey like most by buying 0.001 BTC on a KYC, centralized exchange. After reading our excellent bitcoin privacy guides, you get your own wallet and take ownership of your private keys by transferring that 0.001 BTC to your new wallet. Later on, you buy another 0.001 BTC from a non-KYC source and stick it in the same wallet.
Knowing exactly which 0.001 BTC is from which source enables you to know which UTXO to spend, not spend, perform a CoinJoin on or use when spending with a regulated entity that actively performs chain analysis. It also ensures that the extra effort you went to in obtaining the non-KYC bitcoin is preserved and not destroyed by mixing it in with the KYC sourced ones.
A recent, real world example of why Coin Control is important for your privacy is the sanctioning of the Truckers Convoy Bitcoin addresses in Canada. While we absolutely don’t agree with their cause (vaccines are an amazing invention), imagine if you had 50 UTXO’s in your stash and 5 of them got tied up in this sanctioning somehow.
Coin Control & Labeling would allow you to properly label those 5 UTXO’s and then make sure you never send them to any regulated entity in the future. Most top tier Bitcoin wallets allow for Coin Control as well as Coin Labeling. Wallets such as Sparrow Wallet, Specter Wallet, Electrum, Nunchuk and even Bitcoin Core all fully support both.
Pro Tip: Coin Control can also help you reduce fees as the more inputs you have in your transaction, the larger (in kilobytes) the transaction – and thus fees – will be. There’s also no downside to using Coin Control & Labeling besides just the slight extra hassle of making a note of where the coins originally were received from.
CoinJoin And Its Limitations
As Bitcoin is easily traceable via its permanent and transparent blockchain history, it might seem impossible to “unlink” some bitcoins that you’ve bought from a KYC source. That’s where Bitcoin Mixers like CoinJoin comes in.
Its goal is to mathematically disassociate the ownership of inputs to outputs in a given bitcoin transaction. This is to increase the privacy of the users involved, protect against financial surveillance, and to increase the fungibility of the Bitcoin network as a whole.
Samourai Wallet’s Whirlpool
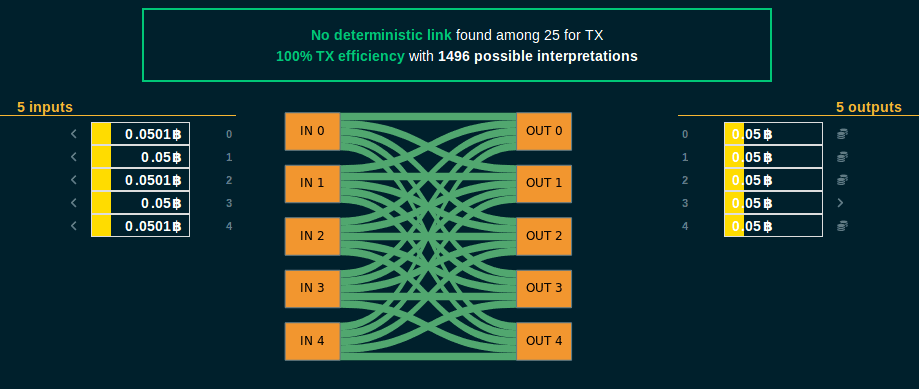
CoinJoin is a trust-less way to combine multiple Bitcoin inputs from one or multiple entities in a single transaction. This makes it more difficult for Chain Analysis firms to figure out which spender paid which recipient(s). It also severs the history of the bitcoins used in the transaction and allows for your privacy to be protected going forward.
There are different types of implementations, each done through different software wallets (some automatically) with their own take on the same basic idea. You have one or more users pool their UTXO’s together into the same transaction that then has many identical outputs (note how all outputs in the image above is 0.05 BTC).
CoinJoin does have a few considerations to look at before you start though:
- There are fees with CoinJoin, so make sure you understand them before starting
- Never use centralized ‘mixers’ that take custody or control of your Bitcoin
- You should run your own Full Bitcoin Node before using CoinJoin for maximum privacy
Pro Tip: Your spending habits after you CoinJoin are very important too and can undo your privacy gains if you do things like combine multiple CoinJoin outputs. For example in the image above, if you recombined all of the 0.05 BTC outputs in another transaction to 0.25 BTC, it would be pretty easy for chain analysis firms to deduce that you still own all those outputs.
>> Deeper Dive: Bitcoin Mixers: How To Master The Art Of Digital Disguise
The Athena Assessment
Advanced privacy in Bitcoin can be difficult for people to get right as it requires a relatively high technical capability as well as a good understanding of How Bitcoin Works. With the introduction of easy to use Full Bitcoin Nodes, automated CoinJoin software, embedded Tor use by default in many wallets and more things are slowly becoming easier though.
Just like with the Internet and its evolution, it’s now trivial for everyday grandmas to instantly download and use end to end encrypted messaging applications like Signal without being the least bit technical. We’re positive that over time this too will happen to Bitcoin and its ecosystem of hardware wallets, wallets, nodes and more.
FAQ
What’s The Most Private Bitcoin Wallet?
This is obviously a subjective question to answer depending on what aspects of privacy are important to you and how much of a trade off between privacy and ease of use you’re willing to take. That being said we recommend Sparrow Wallet for desktop, Blue Wallet for mobile and our top rated Crypto Wallets for the hardware wallet
Where Are Bitcoins Stored?
While many assume they’re stored in your Bitcoin Wallet, they do not store any bitcoins! Instead, Bitcoin Wallets only ever store your private keys which is what gives you access to your bitcoins. Every bitcoin is and always has been located on the Bitcoin network.
What Are Crypto Privacy Coins?
Privacy coins are a class of cryptocurrencies that have been specifically created with enhanced privacy properties built into them as opposed to being added on after the fact. Some of the leading privacy coins you might see are Dash (DASH), Monero (XMR) and Zcash (ZEC), but we don’t recommend using them.
Should You Use A Privacy Coin?
While using privacy coins has been banned in a few countries, most generally operate in a legal grey zone. Wanting financial privacy isn’t a crime, but international and local financial authorities often insist that only criminals use them as a way to justify their new, more strict and invasive laws.
As a result, privacy coins have already been removed from many centralized exchanges due to these over zealous regulations that these companies must abide by. For most people using a privacy coin isn’t required, as you get many similar protections by using Bitcoin in a non-custodial way, backed by your own Full Bitcoin Node that’s connected via Tor.
Can A Bitcoin Wallet Be Traced?
Wallets can generate essentially infinite addresses and none of them are easily linked to one another. As such, tracing a wallet can technically be done, but isn’t nearly as common as tracing an individual Bitcoin Address or UTXO.